Common Product Security Mistakes That Lead to Breaches
Modern digital products are becoming increasingly complex. Today’s applications rely on APIs, cloud infrastructure, mobile integrations, microservices, third-party libraries, containers, and AI-driven features to deliver seamless user experiences. While this…
Penetration Testing for AI and LLM Applications: A Complete Guide
Artificial intelligence is rapidly changing the way businesses operate. From AI chatbots and virtual assistants to enterprise copilots and autonomous AI agents, organizations are increasingly integrating Large Language Models (LLMs)…
Why Manufacturing Is a Prime Target for Cyber Attacks in 2026
The manufacturing sector has become one of the most targeted industries for cyber-attacks in 2026. As factories embrace digital transformation, Industry 4.0 technologies, and interconnected supply chains, they are also…
Why Product Security Testing Is Critical Before Every Release
Product security testing is no longer a secondary step in software development—it is a core requirement for modern applications. With every release introducing new code, APIs, and third-party components, the…
Why VAPT Services Are Critical for Modern Enterprises in 2026
Cyber threats in 2026 are more sophisticated, automated, and persistent than ever before. With businesses rapidly adopting cloud technologies, APIs, AI-driven applications, and remote work environments, the attack surface has…
Common Security Gaps Found in Enterprise Environments
Modern enterprises invest heavily in cybersecurity tools, yet breaches continue to rise. The reason is rarely the absence of security technology — it is the presence of security gaps created by complexity,…
Top SaaS Security Risks in Enterprises and How to Prevent Them
Software-as-a-Service (SaaS) platforms have transformed how enterprises operate by enabling rapid deployment, scalability, and seamless collaboration across distributed teams. Organizations now depend on SaaS applications for critical business functions ranging from communication…
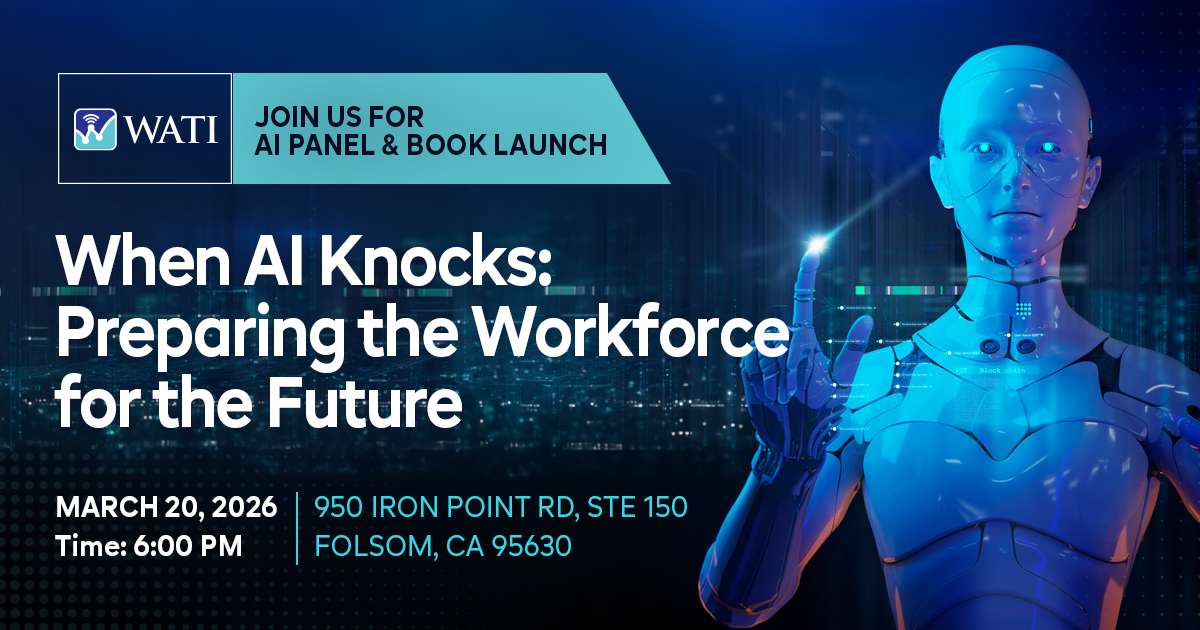
When AI Knocks: Preparing the Workforce for the Future — AI Panel & Book Launch Event
Artificial Intelligence is no longer a future concept — it is actively transforming how organizations operate, how employees work, and how industries evolve. As AI adoption accelerates across sectors, businesses and…
Why Product Security Testing for Startups Matters More Than Ever
Startups today are built for speed. Founders focus on innovation, rapid releases, and market traction, often measuring success by how quickly a product reaches users. While this agility fuels growth,…
Why “No Breaches Yet” Is a Dangerous Security Indicator
In many organizations, security success is often measured by a simple statement: “We haven’t had a breach.” At first glance, this sounds reassuring. Leadership teams interpret the absence of incidents as proof that…
AI-Driven Phishing Attacks: What Every Business Needs to Know
Phishing attacks have long been one of the most common cybersecurity threats, but the rise of AI-driven phishing is fundamentally changing the landscape. Unlike traditional phishing campaigns, which rely on generic messages…